Control Data Access Everywhere
Enforce granular, real-time data access controls across cloud platforms, analytics, and AI workloads without moving data or disrupting users.

The Challenge
Cloud, analytics, and AI have outpaced traditional data controls
Static roles, manual masking, and fragmented tools leave sensitive data exposed across hybrid environments.
Data access sprawl across warehouses, lakes, and AI pipelines
Excessive privileges remain undetected for months
Security teams lack real-time enforcement at the data layer
Solution Overview
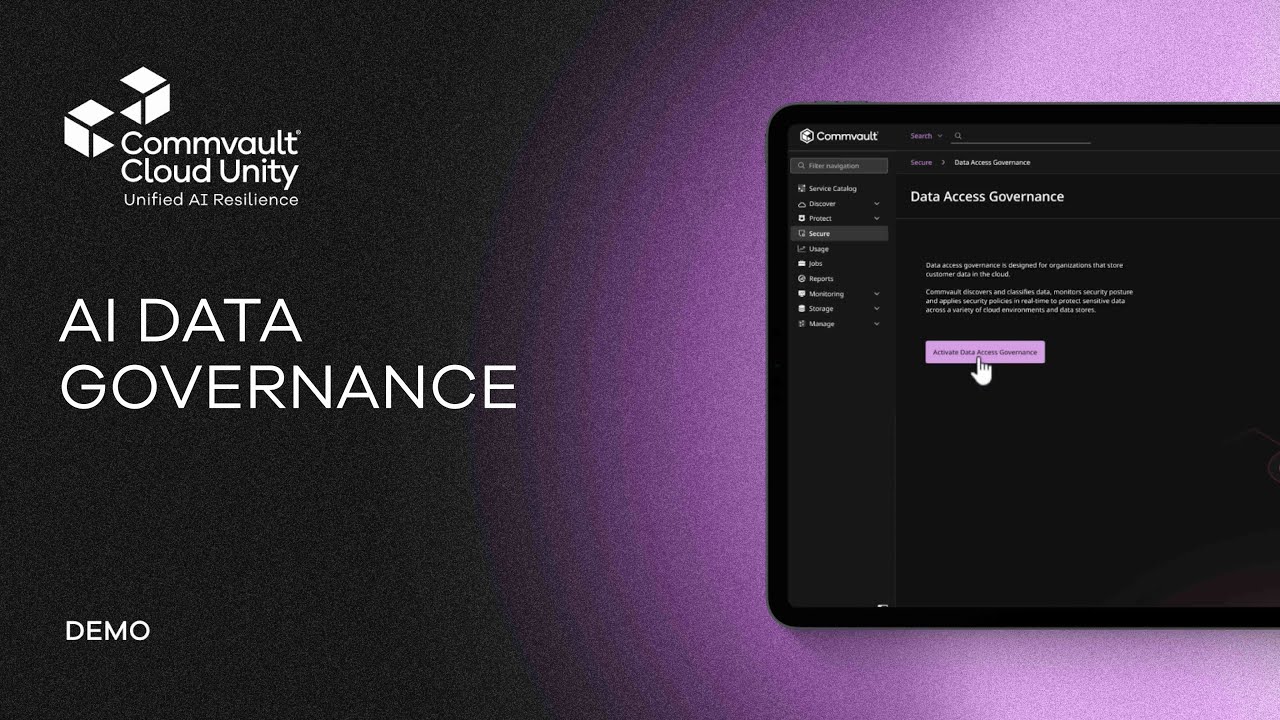
Data Access Governance Enforces Access Controls at the Point of Data Use
See how centralized policy enforcement can safeguard sensitive data across cloud, analytics, and AI workloads.
Why Commvault
Zero Trust for Data
Commvault Data Access Governance delivers real-time, policy-based controls across hybrid environments to reduce exposure without slowing innovation or breaking workflows.
Real-Time Enforcement
Apply granular policies at query time without moving data or rewriting applications.
Unified Policy Control
Centralize access governance across cloud warehouses, lakes, databases, and AI environments.
Full Audit Visibility and Proof
Capture detailed activity logs and context for compliance, investigations, and risk monitoring.
protect
Reduce Sensitive Data Exposure
Minimize excessive access and enforce least-privilege dynamically across structured and semi-structured data sources.

Granular Access Control
Enforce row, column, and attribute-level policies dynamically at query execution.
Dynamic Data Masking
Apply real-time masking based on identity, role, and contextual attributes.
Context-Aware Policies
Adjust access based on user behavior, device posture, or environment.
Just-in-Time Access
Grant temporary, policy-driven access without manual ticketing workflows.
Cross-Platform Enforcement
Govern data across warehouses, lakes, and hybrid databases consistently.
Runtime Policy Engine
Enforce controls inline without requiring data replication or migration.
Comply
Operationalize Data Compliance
Translate regulatory requirements into enforceable policies with auditability across environments.
Centralized Policy Management
Define and manage access policies from a single control plane.
Comprehensive Audit Trails
Capture detailed query logs and access activity across data systems.
Policy-Based Data Classification Integration
Enforce controls based on tags and sensitivity labels.
Regulatory Policy Templates
Accelerate compliance with built-in frameworks for common standards.
Access Reviews & Reporting
Generate reports to support audits and governance processes.
Separation of Duties Enforcement
Limit conflicts of interest across data teams and environments.
Enable
Accelerate AI and Analytics
Empower data and AI teams with access controls that remove friction while maintaining security oversight.

AI Data Access Governance
Govern sensitive data exposure to AI and LLM-based applications.
Developer-Friendly Integration
Safeguard pipelines without changing application logic.
Secure Data Sharing
Enable governed collaboration across internal teams and partners.
Fine-Grained Role Expansion
Avoid over-permissions while supporting flexible data use.
Hybrid Deployment Support
Govern cloud and on-prem environments consistently.
Minimal Performance Impact
Maintain low latency enforcement without disrupting analytics workloads.
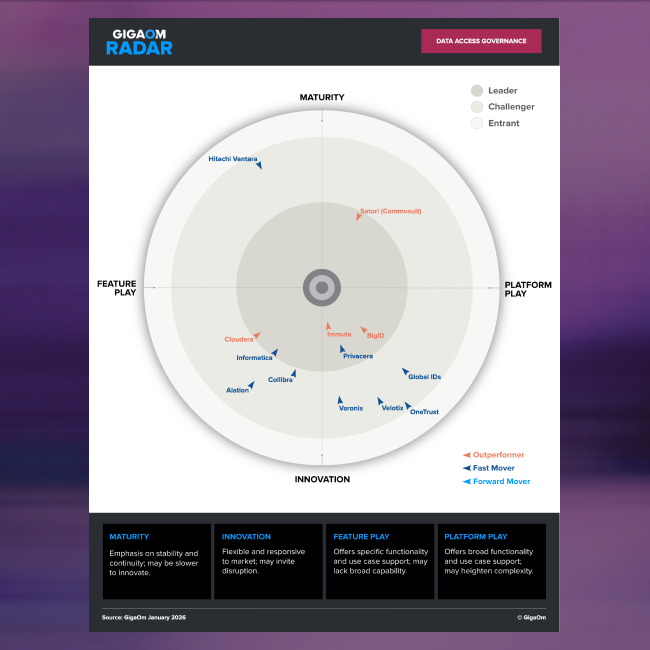
Analyst Recognition
Recognized as a Leader in Data Access Governance
Independent analysts firm GigaOm recognizes Commvault’s Data Access Governance solution as a leader in the Data Access Governance category.
Customer impact
Safeguard sensitive data at enterprise scale

Data Security in the Age of AI
GigaOm Data Access Governance Radar Report

WealthSimple Case Study
Frequently Asked Questions
What is data access governance?
Data access governance is the practice of controlling who can access sensitive data, at what level, and under what conditions, in real time.
It enforces granular policies at the data layer, including row, column, and attribute-level controls, without moving or duplicating data. Unlike traditional data governance, which focuses on cataloging and stewardship, data access governance actively enforces access control at the point of data use across cloud, analytics, and AI environments.
How is this different from IAM?
IAM manages identities and roles, but it does not enforce fine-grained controls at the data level.
Identity and Access Management systems determine who can log into systems or services. Data access governance enforces what users can see inside the data itself. This includes masking specific columns, filtering rows, or applying context-aware policies at query time. It adds runtime protection beyond static roles.
Does this require moving data?
No. Data access governance enforces policies without moving, replicating, or modifying the underlying data.
Controls are applied in real time during query execution, allowing organizations to safeguard sensitive data without redesigning pipelines or duplicating datasets. This approach minimizes operational disruption and avoids performance overhead associated with traditional masking or data relocation strategies.
Can it support AI workloads?
Yes. Data access governance can control which data AI models and LLM-based applications are allowed to access.
It enforces policies on the underlying data sources used by AI systems, reducing the risk of overexposure, prompt leakage, or unauthorized data usage. This enables organizations to adopt AI responsibly while maintaining compliance and least-privilege access principles.
How does this integrate with Commvault recovery?
Data access governance complements Commvault recovery by protecting live data while resilience safeguards backup data.
Commvault recovery enables rapid restoration after ransomware or cyber incidents. Commvault Data Access Governance reduces the risk of breach in the first place by limiting excessive privileges and enforcing least privilege. Together, they provide end-to-end data security and resilience across production and backup environments.
Get Started
Safeguard Data Without Slowing Innovation
See how Commvault Data Access Governance can enforce real-time controls across cloud, analytics, and AI environments.