
Cyber Resilience & Data Security
Can You Prove Your Data Is Recoverable? Anomaly and Threat Detection for Backup Security
Embedding detection into backup and recovery workflows can help organizations validate clean data, reduce reinfection risk, and recover with confidence.
Featured

Can You Prove Your Data Is Recoverable? Anomaly and Threat Detection for Backup Security

Anthropic’s Project Glasswing Makes the Case for ResOps
From Recovery to ResOps™: Building Enterprise Resilience That Scales

The Next Evolution in Cloud Data Protection

Built for Resilience, Optimized for Scale: The Cloud Rewind Architecture
Modernizing Commvault’s Architecture: From Monolith to Scalable Microservices

Anthropic’s Project Glasswing Makes the Case for ResOps

Data Activate: Unlocking the Power of Trusted Data for AI Innovation

AI Agents Are Everywhere. Do You Know What They’re Doing?

Six Things You Might Have Missed at RSAC

Commvault and Microsoft: The Rise of AI Agents in ResOps

Commvault® Extends Identity Resilience to Okta
More stories

Backup and Recovery
All Your Questions Answered

Clumio
Introducing Clumio RansomProtect: More Than Just Backup

Clumio
Improving Amazon EBS backups using EBS direct APIs
Data Protection
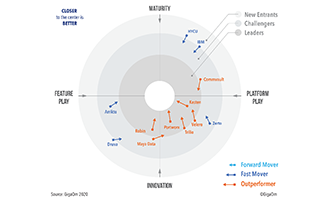
GigaOm Radar for Kubernetes Data Protection publishes report and Commvault is an ‘Outperformer’

Clumio
Protect Your Data from Ransomware: Learn How with Clumio

Clumio
Business Continuity Planning for the Cloud-Native Era

Clumio
The Importance of Recovery Point Objective (RPO) in Your Business Continuity Plan
Clumio